Choosing the right medical app for data security
With rising healthcare data breaches, providers must ensure apps are HIPAA-compliant with proper encryption and security measures to protect patient information.


Popular articles
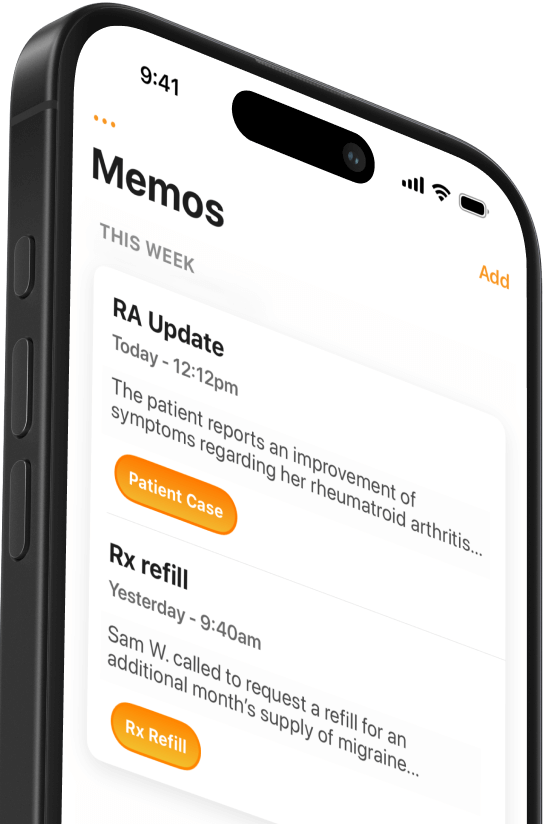
The past few years have seen record numbers of data breaches caused by cyberattacks and ransomware. These breaches have heightened legitimate concerns about the security of protected health information.As a provider, you're already familiar with HIPAA, or the Health Insurance Portability and Accountability Act. This is the legislation passed in 1996 that provides data privacy and security provisions to safeguard medical information.But as digital and mobile health enter your practice, what qualities should you look for in a medical app?We've summarized the basic data security components you should look for in any app that accesses patient health data. The quoted examples come from the FAQ for for Mobius Clinic, a mobile health app that connects providers to their EMR.
What does HIPAA mean for apps?
"Our apps exceed the standards specified by HIPAA and HITECH, the major medical legislation governing data security in the U.S. healthcare industry."
You know HIPAA, but how does this legislation apply to medical apps? Any software that handles protected health information (PHI) needs to be HIPAA compliant, so this should be your litmus test for bringing an app in to your practice.When a software developer says they're HIPAA compliant, it means they've satisfied four main requirements:
- They've put safeguards in place to protect PHI.
- They've limited use and sharing of PHI to the minimum necessary to accomplish the apps function.
- They've set up data security agreements with connected service providers that interact with PHI through the app.
- They've established procedures to limit who can access PHI and trained their employees about how to protect PHI.
This is what Mobius Clinic means when they write, "All of our employees have completed HIPAA-compliance training and their job descriptions necessitate a continual mindfulness of the sensitivity of PHI."
What is HITECH?
The Health Information Technology for Economic and Clinical Health Act (HITECH) was passed in 2009. HITECH has been called "HIPAA on Steroids" because, among other provisions, it spells out tougher data security requirements for all health care organizations and their business associates like app developers.HITECH is mostly known for incentivizing adoption of electronic health records, but it also implemented rules to ensure that this newly digitized health information remains secure.Enforcement is the most significant security provision of HITECH. The rule provides funding for more frequent audits of covered entities (e.g. hospitals) and business associates (e.g. software companies) as well as tougher fines for data breaches.HITECH also extends HIPAA's 1996 privacy and security rules more directly to business associates. This means that software developers, banks, billing firms and health information exchanges are held to the same standards as hospitals and physician practices when it comes to handling PHI.
What about encryption?
"All private health information received, transmitted, maintained, or created is handled with 256-bit encryption using the Advanced Encryption Standard (AES). Protected health information is never stored in an unencrypted state."
In general, any app that connects to patient data should be encrypted.In nearly every case this is assumed when an app says they are HIPAA compliant. HIPAA requires electronic PHI to be encrypted unless the app developer can argue that doing so is unreasonably expensive or difficult. Another exception is if the developer can provide a "reasonable, appropriate and equivalent" alternative to encryption.You may be wondering, what is encryption? Encryption is basically the process of converting readable data (like text) into an encoded form that can only be deciphered with the decryption key. 256-bit encryption is one of the most secure encryption methods, making it virtually impossible to be broken even by the fastest computers.While most HIPAA compliant software will encrypt data, it's useful to confirm that the apps you use to access PHI are taking this precaution.
Additional security measures
"Furthermore, our software contains additional security mechanisms. Those mechanisms include a secondary passcode for access, keeping our data separate from other apps coexisting on a mobile device. Password security and strength is enforced and repeat app access during a given user’s session necessitates re-authentication via passcode. Access to PHI is audited and tracked."
You will notice that some apps claim to be "Beyond HIPAA Compliant," meaning they've deployed additional security measures to protect sensitive health information.These apps should give you an extra level of confidence knowing that the developers are doing everything possible to secure your patients' data.
External audits
"Finally, we are audited by an independent 3rd party, HITRUST, to ensure we conform to the rigid standards expected and required for modern medical software. Don't hesitate to reach out if you have any questions about our independent audit."
Remember that there is no certification process for HIPAA. It is up to the software developer to ensure that their administrative, technical and physical safeguards meet HIPAA compliance requirements.Apps that are serious about data security will often work with an external auditor to assess their compliance.When you see that an app has been audited by an independent third party, you can sleep soundly knowing your patient data are safe.http://45.33.12.216/blog/2017/05/ransomware-complicates-healthcare-cybersecurity/
Related Articles

We Get Doctors Home on Time.
Contact us
We proudly offer enterprise-ready solutions for large clinical practices and hospitals.
Whether you’re looking for a universal dictation platform or want to improve the documentation efficiency of your workforce, we’re here to help.





